Two-factor authentication has become an essential security measure as digital services play a larger role in everyday life. Email accounts, banking applications, cloud platforms, and business systems all rely on authentication to prevent unauthorized access. For many years, passwords served as the primary security mechanism, but modern cyber threats have exposed their limitations.
Two-factor authentication strengthens account security by requiring users to verify their identity using more than one method. By adding an additional layer of protection beyond passwords, it significantly reduces the risk of account compromise, even when login credentials are stolen.
What Is Two-Factor Authentication
Two-Factor Authentication is a security method that requires users to provide two different types of verification before accessing an account or system. These verification steps must come from separate authentication categories, ensuring that a single compromised credential does not grant access.
Typically, 2FA combines:
- A password or PIN (something the user knows), and
- A second factor such as a one-time code, security device, or biometric scan.
This approach prevents attackers from gaining access using only stolen passwords, making it one of the most effective security enhancements available today.

Why Two-Factor Authentication Is Important
Passwords are vulnerable for several reasons. Many users reuse the same password across multiple platforms, making a single data breach potentially damaging across many accounts. Phishing attacks also trick users into sharing their credentials, while automated tools can guess weak passwords at scale.
Two-Factor Authentication reduces these risks by ensuring that access requires more than just a password. Even if an attacker obtains login credentials, they cannot complete the authentication process without the second factor, which is usually tied to a physical device or biometric identity.
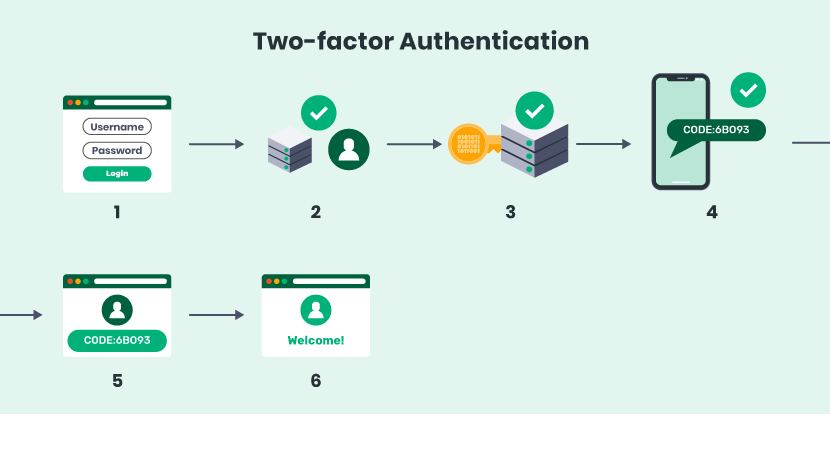
How Two-Factor Authentication Works
Although implementations vary, most 2FA systems follow a standard process:
- The user enters a username and password.
- The system verifies the password.
- A second authentication request is triggered.
- The user provides the second factor.
- Access is granted only if both factors are valid.
This two-step process ensures that unauthorized users are blocked even if they know the password.
Types of Authentication Factors
All authentication mechanisms fall into three main categories. A secure 2FA system always combines factors from two different categories, not the same one.
• Something You Know
This includes passwords, PINs, or security answers. While convenient, this factor is the most vulnerable to compromise.
• Something You Have
Examples include smartphones, hardware security keys, or authentication tokens. This factor provides strong protection because it requires physical possession.
• Something You Are
Biometric identifiers such as fingerprints, facial recognition, or iris scans fall into this category. These are unique to each individual and difficult to replicate.
Common Two-Factor Authentication Methods
• SMS Verification Codes
A temporary code is sent to the user’s registered mobile number. The user must enter the code to complete the login.
Advantages: Easy to use, widely supported
Limitations: Vulnerable to SIM-swap attacks and network interception
• Authenticator Applications
Authenticator apps generate time-based codes directly on the user’s device.
Advantages: More secure than SMS, works offline.
Limitations: Requires setup and backup planning.
• Hardware Security Keys
Physical devices authenticate users through cryptographic verification.
Advantages: Very strong security, resistant to phishing
Limitations: Additional cost and risk of loss
• Biometric Verification
Biometrics authenticate users based on physical traits.
Advantages: Fast and convenient
Limitations: Privacy concerns and occasional false rejections
Where Two-Factor Authentication Is Used
Two-Factor Authentication is widely adopted across industries:
- Email and communication platforms
- Online banking and financial services
- Enterprise and remote work systems
- Cloud services and SaaS platforms
- E-commerce and payment portals
In each case, 2FA reduces the likelihood of unauthorized access and data breaches.
Benefits of Two-Factor Authentication
- Strong protection against account takeover
- Reduced impact of stolen passwords
- Protection against automated login attacks
- Increased user trust and platform credibility
- Cost-effective security improvement
These advantages make 2FA a recommended security practice for both personal and professional use.
Limitations of Two-Factor Authentication
While highly effective, 2FA is not flawless. Some methods, particularly SMS-based verification, can be targeted by advanced attackers. Social engineering attacks may also trick users into approving fake authentication requests. Additionally, some users find 2FA inconvenient if recovery options are poorly designed.
Despite these limitations, 2FA remains far more secure than password-only authentication.
Best Practices for Using 2FA
Use authenticator apps or hardware keys instead of SMS where possible
- Enable backup authentication methods
- Never share verification codes
- Review login alerts and security notifications
- Secure account recovery processes
Implementing these practices ensures that 2FA provides maximum protection without unnecessary inconvenience.
The Future of Authentication
As cybersecurity evolves, authentication systems are moving toward passwordless solutions that rely on secure devices and biometrics. While these technologies are still developing, Two-Factor Authentication remains a practical and reliable defense against modern threats.
Conclusion
Two-Factor Authentication is one of the most effective ways to protect online accounts in today’s digital environment. By requiring two independent verification steps, it significantly reduces the risk of unauthorized access and data breaches. Although no security system is perfect, 2FA provides a powerful balance between usability and protection.
Enabling Two-Factor Authentication wherever possible is no longer optional — it is an essential step toward safeguarding digital identities and sensitive information.
